Null Byte & Null Space Labs Present: Wi-Fi Hacking, MITM Attacks & the USB Rubber Ducky « Null Byte :: WonderHowTo
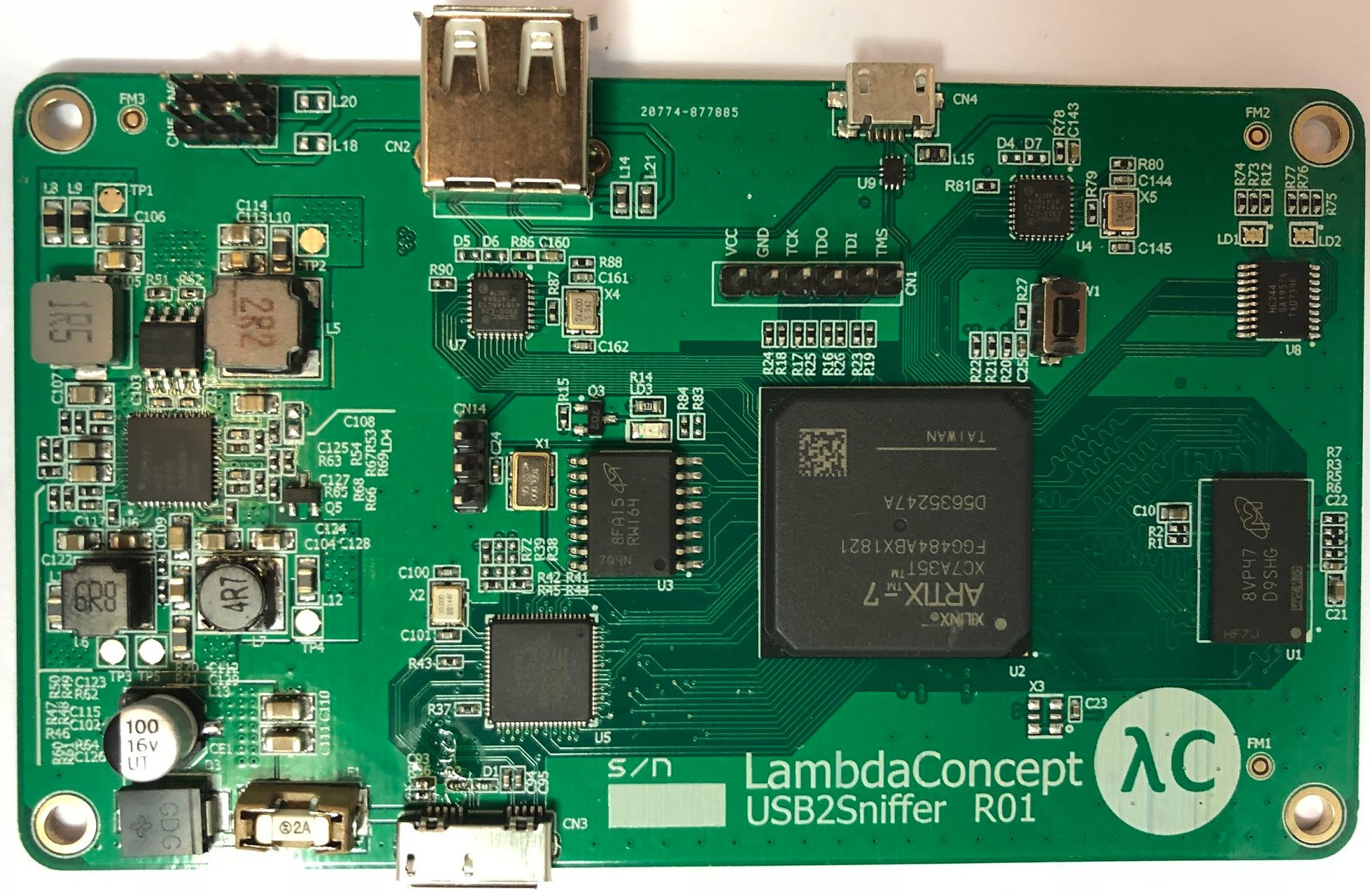
LambdaConcept on Twitter: "This is our new toy: - Artix 7 FPGA - 2 High Speed USB ULPI (male/female) - FT601 USB 3.0 w/ 5Gbps bandwidth - 256MB DDR3 RAM Use cases: -

Dominic Spill on Twitter: "Usb-mitm on a BeagleBone Black relaying an Ubertooth to my laptop. Next task is Wireshark integration with extcap. http://t.co/iu6lE0Q2Nh" / Twitter

Amazon.com: Tripp Lite 6ft HDMI DVI USB KVM Cable Kit USB A/B Keyboard Video Mouse 6' (P782-006-DH) : Everything Else